

When it comes to breaking news for you the fastest and in the most comprehensive and accurate manner, be it from Odisha or beyond, OdishaTV is the best

A meeting of the party was held at Sankha Bhawan where Amar Satpathy was absent. Jajpur MP, party’s district observer, and ticket aspirants like Rajnarayan Mohapatra and Janmejaya Lenka attended the meeting which was reportedly called to placate the dissent.

BJD’s press meet was reportedly aimed at Union Minister Dharmendra Pradhan for his ‘alleged jibe’ at the Chief Minister & BJD president Naveen Patnaik, who was seen in a lungi in a video appeal to voters.

Recently in Puri, BJD’s MP candidate, Arup Patnaik was canvassing for votes at Pipili, when he fainted. Patnaik was immediately hospitalised and recovered later.

Responding to the call of samiti member of Kanchana panchayat, Chitrasen Ghose, over 8,000 BJD workers including sarpanchs of five panchayats joined the BJP.

Animesh Pradhan, the second topper of the 2023 UPSC exam, visited OTV newsroom, sharing insights on his preparation strategies and future aspirations. Animesh emphasized governance for tribal empowerment in Odisha and discussed the challenges faced during his UPSC journey.

A notorious 7-member 'Irani Gang', known for posing as police officers to rob people, was apprehended in Bhubaneswar with Rs 3.5 lakh cash and gemstones. The gang, hailing from Madhya Pradesh, has been linked to numerous robberies across several states.

Prime Minister Narendra Modi, Home Minister Amit Shah, BJP National President JP Nadda, Defence Minister Rajnath Singh, UP CM Yogi Adityanath, Assam CM Himanta Biswa Sarma, MP CM Mohan Yadav, Union Minister Nitin Gadkari and party’s National Vice President Baijayant Panda among other prominent leaders were included in the list.
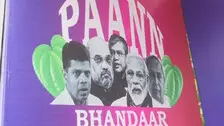
Congress workers opened betel shops to highlight the alleged scams by the BJD and BJP.

Jay Panda took out a massive rally in Mahakalapada from Angulai. The rally covered a distance of 20 kms across seven panchayats and villages.

Expressing his unhappiness over various issues, Krushna Sikaka, a local resident said, "Maoist-related false cases are registered against the Dongrias. Hence, we are being harassed. Such cases should be withdrawn.”

A purported video of BJD’s Puri district observer, Ranendra Pratap Swain has gone viral in which he revealed the reason why the party ticket was not given to Dash.

The STF officials seized brown sugar (Heroin) weighing more than 1.1 Kg (1120 gram) and other incriminating materials from their possession.

Nayak expressed her dissatisfaction with the development. She alleged that a few individuals are responsible because of whom she was denied ticket.

Apart from Bhubaneswar, six other places in Odisha recorded a maximum temperature of 35 degrees and above on Tuesday.

Copyright © 2024 - Odisha Television Limited All Rights Reserved.